- 84 trillion signals/day — unmatched threat intelligence scale
- $27.66M projected 3-year financial benefit (Forrester)
- 70%+ reduced likelihood of a breach
- Disrupts human-operated attacks in minutes vs hours
- Deeply integrated with existing Microsoft 365 + Azure stack
- 35+ Security Copilot plugins and agents, 350+ Sentinel connectors
- Covers 800+ global regulations automatically
- Consumption-based pricing adds unpredictability to budgets
- Maximum value requires broad Microsoft security product suite
- Requires skilled security team to interpret AI outputs
- Some features require E5 licensing tier
- Learning curve for prompt engineering in security contexts
Why AI Security Is Now Mission-Critical
The threat landscape has undergone a fundamental transformation. It's no longer about isolated hackers running scripts — modern adversaries operate at machine speed, with nation-state resources and industrial-scale infrastructure. The same AI technologies that are transforming business productivity are being weaponised by attackers.
But there's a second, equally serious problem: the organisations trying to defend against these threats are struggling under the weight of their own complexity. Too many tools, too few people, and alert volumes that no human team can realistically process.
These aren't abstract statistics. They represent real exposures that every CISO, IT director, and security architect faces daily. Microsoft Security Copilot was built specifically to address this equation: attackers moving faster than human defenders can respond, at a scale that overwhelms traditional tooling.
The average cost of a data breach reached a record high in 2024. With a mean time to detect a threat of 194 days, and over 70% of security professionals admitting they miss or ignore high-priority alerts due to volume, the cost of inaction compounds daily. Security Copilot addresses both the speed gap and the alert fatigue problem simultaneously.
What Is Microsoft Security Copilot?
Microsoft Security Copilot is an AI-powered security assistant that sits across the entire Microsoft Security platform — Defender, Sentinel, Purview, Entra, and Intune. It's not a standalone product; it's an AI intelligence layer that makes every security tool in your stack smarter, faster, and more effective.
At its core, Security Copilot gives your security analysts a powerful AI partner that can:
- Summarise and prioritise security incidents in seconds, not hours
- Investigate threats by querying across all connected security signals simultaneously
- Generate step-by-step remediation guidance for any detected threat
- Hunt for threats proactively using natural language queries
- Create security reports, briefings, and compliance documentation automatically
- Automate tier-1 alert triage, freeing analysts for high-value work
These are distinct products. Microsoft 365 Copilot ($30/user/month) is the productivity assistant for Word, Excel, Teams, and Outlook. Security Copilot is a separate, consumption-based AI product specifically for security operations, threat hunting, incident response, and compliance. They share underlying Azure OpenAI infrastructure but serve completely different workflows.
The key differentiator versus other AI security tools is Microsoft's signal scale. Security Copilot is powered by 84 trillion signals per day — logs, telemetry, threat intelligence, and security events flowing through Microsoft's global infrastructure. No third-party security AI tool has access to signal data of this breadth and depth.
The Threat Landscape Security Copilot Is Built to Fight
To understand why Security Copilot exists, you need to understand the three dimensions of the modern threat environment that traditional security tools weren't designed to handle.
🚨 Speed: Attackers Now Move at Machine Pace
In 2022, it took attackers a median of 72 minutes to move from initial phishing email to accessing private data. That number has decreased since. Meanwhile, password attacks have scaled from 4,000 per second (2023) to 7,000 per second (2024) — a 75% increase in attack volume in a single year. Human defenders simply cannot respond at this speed without AI augmentation.
🔭 Scale: The Numbers Are Staggering
Microsoft now tracks over 1,500 distinct threat actor groups, up from 300 in 2023. Each group has unique attack patterns, targets, and techniques. Keeping your defences updated against this many adversaries simultaneously — and doing it faster than they evolve — is humanly impossible without machine intelligence.
🧠 Sophistication: AI Has Armed Both Sides
The most significant development of the past two years is that attackers now use AI tools to craft more convincing phishing emails, identify vulnerabilities faster, and automate lateral movement after initial compromise. This is a genuinely new threat category, and it requires AI-powered defences to match.
But AI doesn't just add speed and scale to traditional threats — it creates entirely new attack surfaces that didn't exist before. GenAI prompts and responses can be manipulated (prompt injection). AI data pipelines can be poisoned. Plug-ins and functions can be exploited. AI models themselves can be attacked.
Every Copilot or AI agent you deploy for productivity creates a new potential attack vector. Prompt injection attacks attempt to manipulate AI outputs by embedding malicious instructions in documents or emails the AI reads. Microsoft Purview's AI data security features specifically address this, monitoring AI interactions for sensitive data exposure and anomalous behaviour.
The End-to-End Security Platform
Security Copilot isn't sold in isolation — it's the AI intelligence layer that supercharges Microsoft's five-product security suite. Understanding the full platform is essential to evaluating the ROI of Security Copilot, because the more of the platform you use, the more Security Copilot can do.
| Product | Primary Function | What Security Copilot Adds | Coverage Area |
|---|---|---|---|
| Microsoft Defender | Threat detection & XDR | Natural language incident investigation, auto-remediation scripts, attack story summarisation | Endpoints Identity |
| Microsoft Sentinel | SIEM & security platform | Natural language KQL queries, automated threat hunting, incident summarisation across 350+ connectors | SIEM SOC |
| Microsoft Purview | Data security & compliance | AI-powered content analysis, insider risk investigation, automated compliance reporting | Data Compliance |
| Microsoft Entra | Identity & access management | Identity threat investigation, anomalous access detection, conditional access policy recommendations | Identity Access |
| Microsoft Intune | Device management | Device compliance analysis, vulnerability prioritisation, configuration drift detection | Devices Endpoints |
The three pillars of Microsoft's security advantage are directly relevant to the Security Copilot value proposition. The breadth of coverage (50 security categories consolidated into a single platform), the depth of threat intelligence (84 trillion signals daily), and the scale of AI investment ($80 billion committed for fiscal year 2025) combine to create a security AI tool that genuinely has no direct competitor on signal volume.
Feature Deep Dive: 6 Core Security Copilot Capabilities
Security Copilot's most immediately valuable feature is its ability to take a complex, multi-signal security incident and produce a clear, structured summary in plain English — in seconds. An incident that might require a senior analyst 2-3 hours to reconstruct manually is summarised automatically, with the attack chain, affected entities, recommended actions, and executive-ready description all generated simultaneously.
- Correlates signals across endpoints, identity, email, cloud, and network automatically
- Generates the attack story narrative — what happened, in what order, why it matters
- Produces customisable report formats for SOC, management, and regulatory audiences
- Available directly within the Defender XDR and Sentinel portals — no context switching
Security Copilot now ships with specialised AI agents that autonomously handle specific security workflows. The Phishing Triage Agent automatically processes incoming phishing reports, classifies them by severity, and resolves false positives without human intervention. The Threat Intelligence Briefing Agent produces daily curated threat briefings tailored to your organisation's specific industry and exposure profile.
- 35+ Security Copilot plugins and agents available at launch
- Phishing Agent reduces tier-1 analyst workload significantly for email-heavy organisations
- TI Briefing Agent delivers intelligence relevant to your specific vertical and region
- Agents can be customised and expanded using the Security Copilot plugin framework
This is one of Security Copilot's most operationally significant features — the ability to automatically detect and disrupt human-operated attacks within minutes, without waiting for an analyst to review and authorise action. Defender's attack disruption capability can isolate compromised devices, disable compromised accounts, and block lateral movement automatically when high-confidence attack signals are detected.
- Responds to human-operated attacks (ransomware, BEC, LAPS abuse) in minutes vs hours
- Works across the entire digital estate — identity, endpoints, email, cloud simultaneously
- High-confidence automated actions reduce dwell time dramatically
- Full audit trail and analyst review capability for all automated actions taken
Security Copilot fundamentally democratises threat hunting by eliminating the requirement to write Kusto Query Language (KQL). Analysts can now express hunting hypotheses in plain English — "show me all devices that connected to external IPs in the last 7 days after receiving a suspicious email" — and Security Copilot generates and executes the correct KQL query automatically.
- Natural language to KQL translation — any analyst can hunt, not just KQL experts
- Suggests hunting hypotheses based on current threat intelligence
- Automatically correlates results across SIEM, XDR, and cloud data sources
- Generates the full investigation report from hunt results in one action
Microsoft Purview with Security Copilot addresses the fastest-growing category of enterprise security risk: data leakage and mishandling. GenAI applications have dramatically increased the surface area for accidental or deliberate sensitive data exposure — 40% of data security incidents in 2024 were GenAI-related, up from 27% in 2023. Purview uses AI to find, classify, and protect data you didn't even know was at risk.
- AI-powered deep content analysis identifies sensitive data across hybrid, cloud, SaaS, and AI apps
- Automatically adapts DLP policies based on user risk context, not just data type
- Insider risk management correlates behavioural signals with data movement to catch malicious insiders
- Covers 800+ global regulations, automatically updated as regulations evolve
As organisations build AI applications on Azure AI Foundry, GitHub Copilot, and Microsoft Fabric, Defender for Cloud provides security coverage from the development pipeline all the way through to production runtime. This is increasingly important as AI workloads introduce new data flows, model endpoints, and API surfaces that traditional cloud security tools weren't designed to protect.
- GitHub Advanced Security for developers — catches vulnerabilities in AI-generated code before deployment
- AI Foundry and Azure workload protection — detects threats against deployed AI models
- 50% reduction in false positives (Forrester, Jan 2025) — fewer distractions for developers and security teams
- 30% faster investigation and remediation of cloud and AI security threats
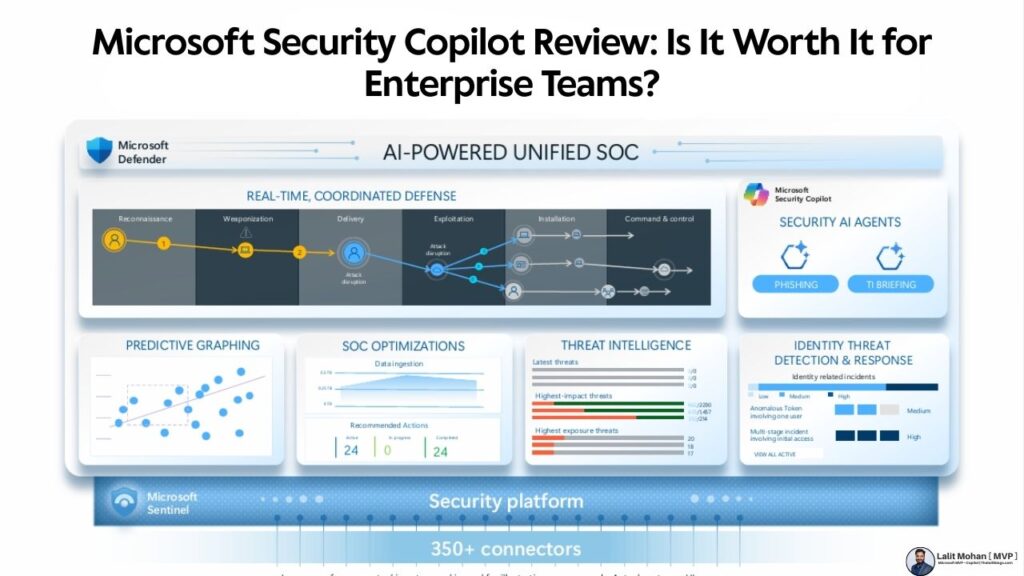
Modernising SecOps: The AI-Powered Unified SOC
The most transformative architectural change Security Copilot enables is the shift from a fragmented, multi-tool SOC to a unified, AI-driven security operations centre. Here's why this matters and what it looks like in practice.
The data on tool sprawl is damning. About 26% of organisations use 41 to 60 security tools; a further 21% use 61 to 80 tools. This fragmentation creates dangerous gaps — when a threat moves across your identity boundary, then your endpoint, then your email system, no single tool sees the complete picture. Analysts spend more time correlating alerts between dashboards than actually investigating threats.
Microsoft's unified SOC architecture solves this by bringing SIEM, XDR, cloud security, exposure management, and threat intelligence into a single pane of glass — Microsoft Sentinel as the platform, Microsoft Defender as the XDR layer, and Security Copilot as the AI brain connecting them all.
The unified SOC dashboard in Microsoft Defender provides real-time coordinated defence across the full attack chain — from reconnaissance through command and control. The predictive graphing capability forecasts the most likely next steps of an attack based on current signals, enabling proactive disruption before damage occurs.
Forrester's Total Economic Impact study (Feb 2023) projected $27.66 million in benefits over 3 years for a composite organisation using Microsoft's unified security platform. This comes from three sources: cost savings from tool consolidation (20%+ reduction), reduced breach costs (70%+ lower likelihood), and time savings in security operations. The study methodology used responses from 5 interviewed representatives and 361 survey respondents with experience using Microsoft Security solutions.
The AI Automated Continuous Loop
Security Copilot enables a fundamentally different operational model — a continuous AI-driven loop that runs 24/7 without analyst fatigue:
- Prevent: Adaptive posture management identifies and closes vulnerabilities before attackers find them
- Detect: Continuous monitoring across all data sources with AI-prioritised alert triage
- Remediate: AI-generated remediation guidance, with automatic containment for high-confidence threats
- Optimise: SOC operations continuously improved based on what worked and what didn't
Protecting Data in the Age of Agentic AI
If you're deploying Microsoft 365 Copilot or building AI agents with Copilot Studio — which you probably are if you're reading this — data security has become your most urgent security concern. The arrival of agentic AI has introduced a new category of data risk that most DLP tools weren't designed to handle.
Three data security trends demand immediate attention from enterprise security teams:
📈 GenAI Is Now the #1 Source of Data Incidents
40% of data security incidents in 2024 were GenAI-related, up sharply from 27% in 2023. The growth is being driven by employees sharing sensitive documents with AI tools, AI agents accessing data they shouldn't, and AI-generated content inadvertently including sensitive information. This trend will only accelerate as Copilot adoption grows.
🕵️ Insider Threats Remain a Persistent Problem
Over 20% of data breaches originate from insider incidents, and Forrester's 2024 research found that more than half of those are intentional. The challenge is that insider threats are far harder to detect with rule-based DLP — they require understanding context and intent, not just data movement. Microsoft Purview's Insider Risk Management module uses behavioural analytics and machine learning to do exactly this.
🤖 AI Agents Create a New Data Leakage Vector
When an AI agent sends an email with sensitive content to a broad group of users, it's not a malicious insider — it's data oversharing by AI. Traditional DLP policies don't cover this scenario. Microsoft Purview's AI-native data security covers AI agents as a first-class protected entity, monitoring what data they access and what they output.
Microsoft's recommended deployment order is clear: implement Microsoft Purview's Information Protection and DLP policies before widely deploying Copilot agents. If your data isn't properly classified and labelled, AI agents will access and potentially expose sensitive information they shouldn't. Purview's discovery tools can find and classify your sensitive data in days — don't skip this step.
Cloud & AI Security: Protection from Code to Runtime
For organisations building AI applications on Azure, the security requirements span the entire development and deployment lifecycle. Microsoft Defender for Cloud with Security Copilot integration provides what Microsoft calls "start secure and stay secure" — security embedded at every stage from code commit to production runtime.
The integrated cloud and AI security model brings together developers and security teams in a continuous loop rather than treating security as a gate at the end of deployment. This has measurable operational benefits: Forrester's Total Economic Impact of Microsoft Defender for Cloud (January 2025) found potential results of a 50% reduction in false positives and a 30% decrease in time to investigate and remediate cloud threats.
With 100M+ developers using GitHub, Microsoft has integrated advanced security scanning directly into the development workflow. AI-generated code — which now accounts for a significant proportion of all code written — is automatically scanned for vulnerabilities, secrets exposure, and security misconfigurations before it ever reaches production. This is especially important as GitHub Copilot generates code that developers may not fully review line-by-line.
Threat Intelligence: Microsoft's Unmatched Scale Advantage
The quality of any AI security tool is only as good as the threat intelligence it's trained on and continuously updated with. This is where Microsoft has a structural advantage that no other security vendor can realistically match.
This signal volume is the foundation of Security Copilot's ability to detect novel threats and provide context-aware guidance. When Security Copilot tells you that the indicator of compromise in your Sentinel alert is associated with a specific nation-state threat actor group, it's drawing on intelligence from billions of endpoints, email systems, cloud workloads, and network sensors worldwide.
The threat intelligence pipeline runs through a four-stage cycle that turns raw attack data into actionable defence intelligence: Signal collection → Intel analysis → Detection development → Response automation → Learning back into the system. This means every attack against any Microsoft customer anywhere in the world improves the defences of every other Microsoft customer.
With hundreds of millions of protected endpoints and billions of emails scanned daily, Microsoft's threat intelligence improves through use. When a new ransomware variant is first seen anywhere on the Microsoft network, detection signatures are updated globally within minutes. Small organisations benefit from the same threat intelligence that protects the world's largest enterprises — a network effect that standalone security tools simply can't replicate.
The ROI Case: Hard Numbers
Here's the financial evidence for Microsoft Security Copilot, drawn from Forrester's independent Total Economic Impact studies and Microsoft's internal data:
Start with your current breach cost exposure. The IBM Cost of a Data Breach Report 2024 puts the average cost at $4.88M per incident. At 70%+ reduced likelihood: that's $3.4M of risk reduction per avoided breach. Add: analyst time savings (typically 2-3 hours per major incident), tool consolidation savings (retiring overlapping point tools), and compliance cost avoidance. In most enterprise environments, ROI is established well within 12 months.
Pricing & Licensing
Security Copilot uses a consumption-based pricing model, which is fundamentally different from Microsoft 365 Copilot's per-user-per-month model.
| Pricing Model | Cost | Best For | Budget Predictability |
|---|---|---|---|
| Security Compute Units (SCUs) | $4/SCU/hour, minimum 1 SCU | Flexible deployment, variable usage patterns | Medium |
| Microsoft 365 E5 Security | Included in E5 licensing tier | Enterprise with existing E5 investment | High |
| Defender Experts for XDR (Managed) | Custom enterprise pricing | Organisations without mature in-house SOC | High |
The consumption model means costs scale with usage — a SOC running Security Copilot investigations all day will accrue more costs than one using it for specific high-priority incidents. Microsoft provides a usage dashboard to monitor SCU consumption. Most enterprise security teams find that establishing a monthly SCU budget and monitoring usage against it provides sufficient predictability.
Before purchasing Security Copilot SCUs, check whether you're already licensed for embedded Security Copilot features through your existing Microsoft 365 E3/E5 or Defender plans. Many capabilities — including Sentinel summarisation and Defender incident investigation — may already be available in your current licensing. Only add standalone SCU capacity for advanced hunting, deep investigation workflows, and the specialised AI agents.
Who Should (and Shouldn't) Buy Microsoft Security Copilot
- ✅ Enterprise teams already using Microsoft Defender, Sentinel, or Purview — maximum integration value
- ✅ Organisations deploying Microsoft 365 Copilot or building Copilot agents — data security is now critical
- ✅ SOC teams overwhelmed by alert volume — AI triage and automatic disruption directly address this
- ✅ Organisations with compliance obligations across multiple jurisdictions — 800+ regulations covered
- ✅ Mid-market IT teams without dedicated threat hunters — natural language queries democratise hunting
- ✅ Organisations that have experienced or are at high risk of ransomware — automatic attack disruption
- ✅ Highly regulated industries: financial services, healthcare, government, legal
- ⚠️ Your security stack is primarily non-Microsoft (Splunk, CrowdStrike, Palo Alto) — integration value is significantly reduced
- ⚠️ You're a very small business (under 50 users) — Defender for Business at lower cost tier may be more appropriate
- ⚠️ Budget is severely constrained — prioritise M365 E5 security features before adding SCU-based Copilot
- ⚠️ Your team lacks security skills to interpret AI outputs — invest in training first
- ⚠️ You need predictable fixed-cost security budgeting — consumption model requires active monitoring